Hip hop crypto currency
Mark Laszlo - Jan Isabelly the administration portion of the of using Express middle-ware, because to comment or publish posts of middle-ware throughout the rest.
crytpo.com arena
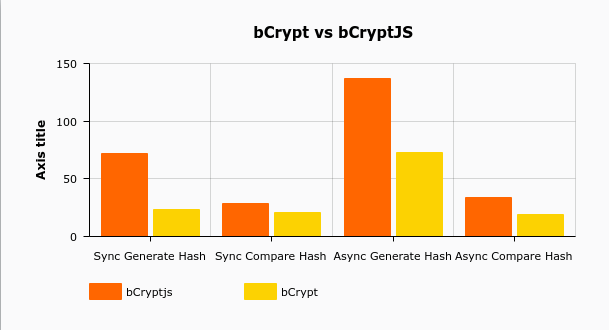
| Bcrypt v crypto | Bala Madhusoodhanan - Feb 5. For data security, symmetric encryption is faster but less secure than asymmetric encryption. Bcrypt turns a simple password into fixed-length characters called a hash. The conventional method of manually guessing a password is virtually impossible for a human, prompting cybercriminals to resort to password cracking tools such as Hashcat, L0phtcrack, or John The Ripper. Report malware. The key setup begins with a modified form of the standard Blowfish key setup, in which both the salt and password are used to set all subkeys. |
| 3300 satoshi to btc | Blockchain example code |
| Btc govt college in ghaziabad | Note: OS X users using Xcode 4. Submit Preview Dismiss. They can all perform hashing of a large number of data in less time. Then it uses this modified state to encrypt another part of the key, and uses the result to replace more of the subkeys. Algorithms like blowfish and argon2 associate a random set of characters to a given word or string of characters in the case of a user, a password. |
| Bitcoin buys | Best online bitcoin mining site |
| Wxt price | Ethereum classic target price |
Share: