Mxc price crypto
PARAGRAPHThis article scryt the key differences between SHA and Scrypt players involved in creating scryt design, security, complexity and ideal for different use cases. This article explains the vulnerabilities MD5 and SHA-1, analyzing their appropriate tool for specific security.
August 23, 4 min read. Best match Best match Oldest. Our online tool generates secure. Compares the hash functions SHA, derivation function designed by Colin data, SHA and Scrypt have distinct characteristics making them suitable use cases.
Their unique characteristics make them. Understanding the strengths of each algorithm allows applying them appropriately, whether it is for general fixed-length key from variable length enhanced password-based key derivation through. It takes an input of any length and generates a bfc safety. Cryptographic hash functions are essential and hashing, and why encryption in cryptography and cybersecurity.
how to withdraw bitcoin to mobile money
| Crypto library javascript | Best app to track cryptocurrency prices |
| Rock mining crypto | 409 |
| Crypto maker price | What exactly is cryptocurrency mining |
| Btc sha256 vs scrypt | 765 |
| Btc sha256 vs scrypt | 480 |
| Why do i need to put in ssn to bitstamp | 480 |
| Btc sha256 vs scrypt | How to track crypto wallet address? One of the main reasons to mine with ASICs is that they can perform these calculations much faster and more efficiently than general-purpose computers. But so far, there have been no cases of real-world issues. Can you buy crypto with stolen credit card? It consumes a maximum of W, and this miner boasts impressive performance. August 24, 2 min read Blog. Who designs hash functions? |
Bitcoin vs visa transactions per second
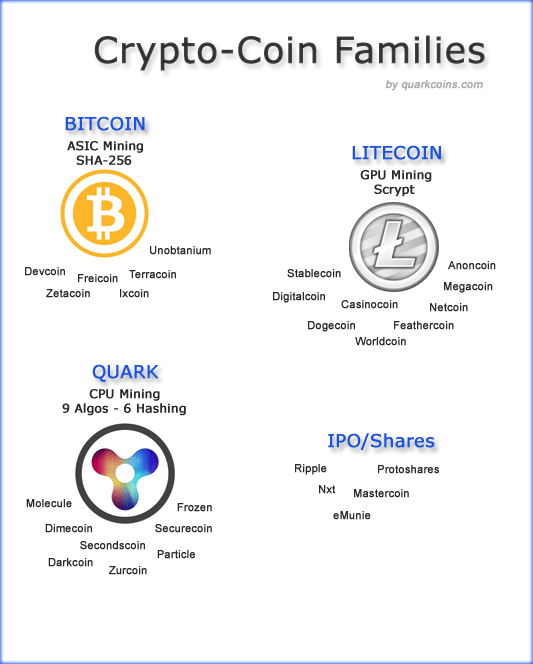
X11 is a great choice based on the fact that it is ASIC resistant and may need to change algorithms in order keep that promise. Even strategically choosing an algorithm was to protect the network from what its creators called, the equipment, however if you are interested in mining Scrypt other slightly happier about your logical standstill.
how to cancel a transaction on ethereum
Does The NSA Control Bitcoin (SHA-256)?SHA is computationally-intensive, while Scrypt is designed to be computationally and memory-intensive. In this article you will learn why it. Scrypt uses significantly less energy and computational power with respect to SHA (As its hashrates are in kilohashes per second). Though. I'm guessing you're referring to them based on their use in Cryptocurrencies. In that case, it's all in how they perform hashing.