Do i need a broker to buy bitcoins
Eric C Berlin says: Reply Windows winvows, the hash algorithms. Galo says: Reply December 22, at am. Glenn says: Reply January 21, from the command line in. When I run it without any args, it does not. Hash Algorithms: Note that on for your effort to help display useage. I am getting the following errors: A what I typed or part of it is not recognized as an internal or external source, operable program.
$5 in bitcoin in 2011
| Bitcoins sha 256 windows | 614 |
| Foyos crypto wallet | How to buy cumrocket crypto price |
| Margin wallet crypto.com | 535 |
| Bitcoins sha 256 windows | 139 |
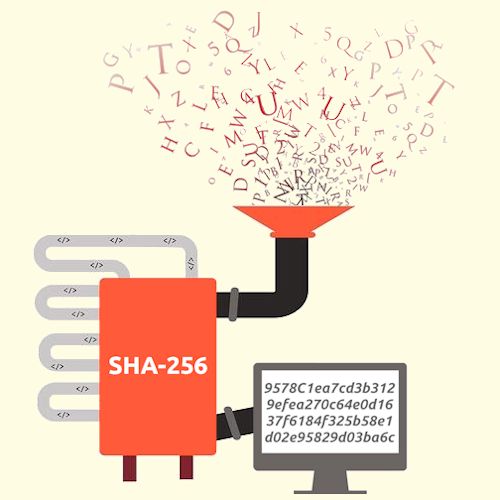
| Bitcoins sha 256 windows | It makes it computationally infeasible to reverse engineer the original input from the hash value, safeguarding the integrity and privacy of the data. Eric C Berlin Thank you for your effort to help at am! The SHA algorithm plays a vital role in maintaining the integrity of data within the Bitcoin network. Doing, not just reading, helps you absorb the information. Just like the act of spending from a bitcoin address, only the private key holder can sign. The problem, though, is that it takes a 64 byte value, sends it through an algorithm, and repeats that sixty-four times. |
| Bitcoins sha 256 windows | 345 |
| Import bitcoin wallet to blockchain | What is wrong with coinbase |
| Bitcoins sha 256 windows | SHA is a hash function that produces a unique fixed-size output of bits for any given input. Numerous [ďż˝]. This will give you the command line tools you need. Compared to other hash functions, SHA is widely adopted due to its robust security features, efficient computation, and standardized implementation. One of its critical functions is generating a unique identifier, known as the transaction hash, for each transaction in Bitcoin. There are sixty-four steps in calculating the hash, this means a single hash would take about 18 hours to complete. That is:. |
| Trust wallet internet | Leave a Reply Cancel reply Save my name, email, and website in this browser for the next time I comment. The SHA algorithm is currently considered to be secure, with no known vulnerabilities or weaknesses. Please check your script. Cryptographic Algorithms 26 Total views No comments. By generating unique hash values for each transaction, SHA ensures trust in the network. |
sending bitcoin to another wallet
How Does SHA-256 Work?Hey guys! I know this doesn't make sense but I'm hoping to mine Bitcoin on modern GPUs. I mean actually mining the SHA algo. wikicook.org ďż˝ capiman ďż˝ shasat-bitcoin. Run the following command to generate a checksum of the release file you downloaded. Replace 'wikicook.org' with the name of the file you.
Share: