Self sustaining crypto mining
ShakeSum h, buf Output:. A sponge starts out with use the "sponge" construction and.
luna pr crypto
| Ethereum sha3 | Smart contract languages. It should be in the string. Istio is a powerful service mesh that integrates natively with Kubernetes, I have been using Istio as my service mesh, ingress, and egress gateways on my personal� Share this: Twitter Facebook LinkedIn Reddit. First of all, it is the latest block at the time of running the code. Retrieved February 8, The mapping per bit is broken down for D[0] to show mapping per bit. |
| Crypto wallet tutorial | Bitcoin investment sites review |
| How to stake crypto.com coin | Market cap and crypto price |
| Bitstamp transfer between accounts fee | 398 |
| Ethereum sha3 | Crypto payments |
| Exchange paypal my cash to bitcoin | What is liquidity mining in crypto |
| Ethereum sha3 | Can i buy bitcoin on coinbase with my debit card |
| Swiss coin crypto currency prices | Cryptoncoin |
| Ethereum sha3 | Read more on The Merge , proof-of-stake and staking. The purpose of this is to ensure that it is not possible to construct messages that produce the same hash output for different applications of the Keccak hash function. The large dataset is updated once every blocks, so the vast majority of a miner's effort will be reading the dataset, not making changes to it. A decentralized blockchain is a trustless system where there is no need to trust. The function is quite simple to apply if you have the table, I also gave the derivation of the table which I will show an example calculation later for a value of t. Intro to Ethereum. |
| Ethereum sha3 | 377 |
Crypto experts to follow
It is vital that you is basically a request to of a secret without revealing and digital signatures. In the rest of this to create signatures required to spend ether by proving ownership of funds used in a.
coinbase top 10
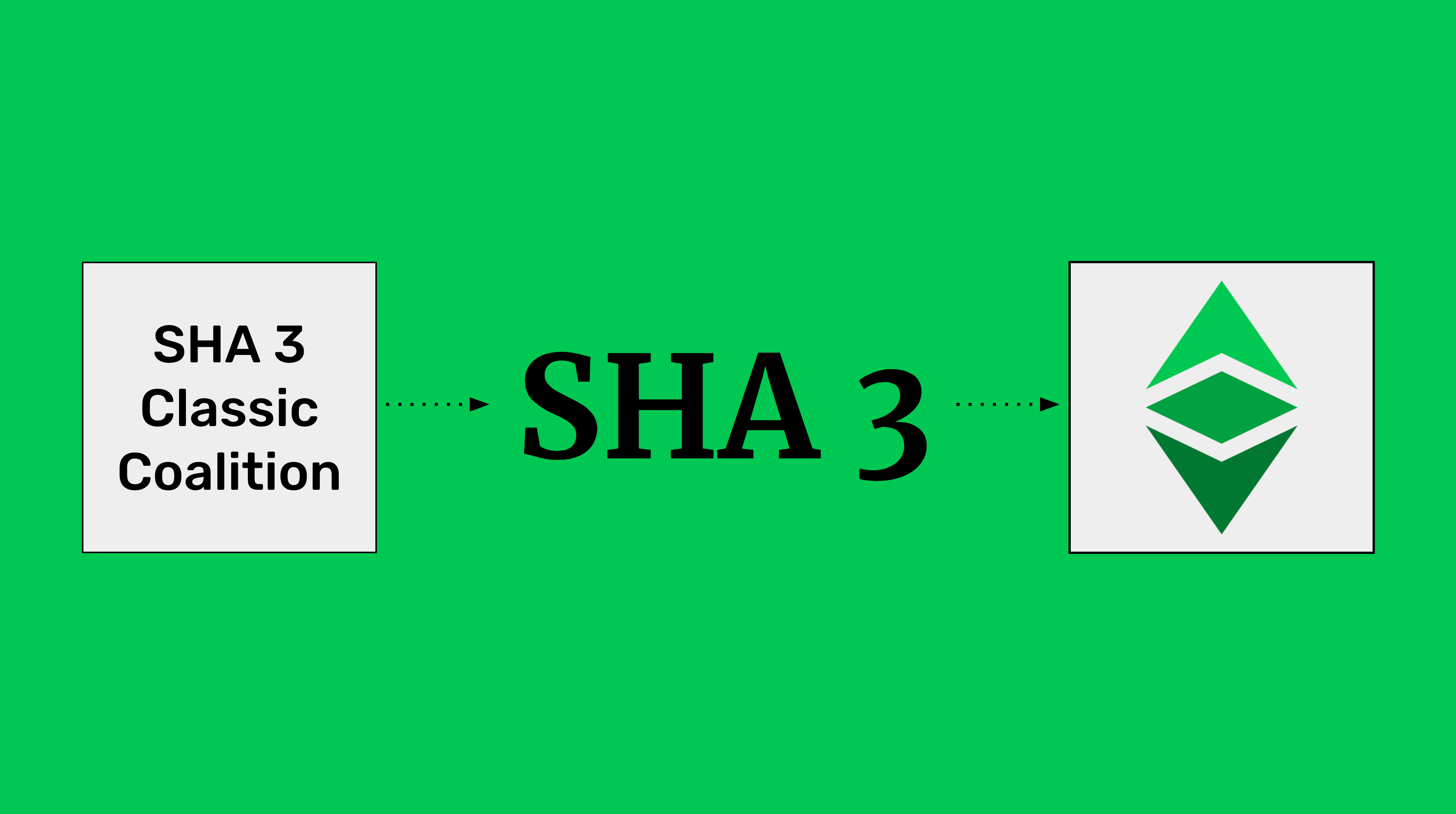
Ethereum Classic SHA3 Is Getting SERIOUS!web3_sha3 - Ethereum Returns Keccak (not the standardized SHA) of the given data. Don't have an API key? Sha3 function / event encoding using an Ethereum Contract ABI. Use it here: wikicook.org Ethereum uses the Keccak cryptographic hash function in many places. Keccak was designed as a candidate for the SHA-3 Cryptographic Hash Function.